Manipulating php.ini
Many of the advices in this guide require you to edit the php.ini file, found in your server’s PHP install folder (not in PrestaShop’s folder).
Not all hosts will allow you to edit or even access this file, so contact your host if you cannot access it.
For instance, you probably won’t have access to php.ini on a shared hosting. If your host doesn’t provide the required configuration by default and you cannot touch php.ini, then you should either move to a dedicated hosting, or change to a more permissive host.
Still, editing php.ini remains a technical and advanced action. If your shop does currently work well, there’s no need for you to touch that file, let alone change host.
Editing the PHP configuration requires you to change some values in the php.ini file, most of the time from “On” to “Off” or vice versa. The file contains a lot of documentation for each line: be sure to read the ones pertaining to your changes, in order to better understand them. Be careful of what you edit, as this has a direct impact on the way PHP runs, and therefore on your servers stability and even security.
Required settings
In order for PrestaShop 1.6.x to run properly, your PHP installation must feature the following settings and libraries:
- MySQL (or Percona Server, see “Improving PrestaShop’s performances” section below).
- GD library.
- Dom extension.
allow_url_fopen.
The MySQL extension enables to access your data. PrestaShop simply cannot work without it.
You can also use the drop-in replacement Percona Server, which offers better performance than the standard MySQL server.
The GD library enables PHP to dynamically manipulate images. PrestaShop uses it to resize and rework the image files that are uploaded (watermarking, trimming, etc.). Without images, an online shop loses most of its interest, so make sure that GD is enabled!
The Dom extension enables to parse XML documents. PrestaShop uses for various functionalities, like the Store Locator. It is also used by some modules, as well as the pear_xml_parser library.
The allow_url_fopen directive enables modules to access remote files, which is an essential part of the payment process, among others things. It is therefore imperative to have it set to ON.
In short, it is imperative to have the following directives set to the indicated values:
extension = php_mysql.dllextension = php_gd2.dllallow_url_fopen = On |
Recommended settings
Your PHP installation should feature the following settings and libraries, for best experience:
- GZIP support.
- Mcrypt library.
register_globalsdisabled.magic_quotesdisabled.allow_url_includedisabled.- Safe mode disabled.
Having GZip support enables the web server to pack web pages, images and scripts before sending them to the browser. This makes navigating the shop faster, and therefore a more agreeable experience.
The Mcrypt provides PHP with a hardened security layer, which enables the use of more hashing and cryptography algorithms.
The register_globals directive, when enabled, defines all environment variables (GET, POST, COOKIE, SERVER…) as global variables. It is unsafe to use unset variables, because a user could easily set a value into this variable by using the GET method, for example. It is therefore imperative to set register_globals to OFF.
The magic_quotes directive automatically escapes (or “adds antislashes”, see http://php.net/manual/en/function.addslashes.php ) to all special character sequences (', ", \, NULL) for all environment variables (GET, POST, COOKIE, SERVER…). This option must be set to OFF because it will addslash each variable even if it does not need to be addslashed. Moreover, some Web applications overlook this option, so some variables could be addslashed twice, resulting in corrupted data.
The allow_url_include directive is used to allow to include any file via the require and include statements, even if it does not come from your Web server. This option must be set to OFF, because if one application on your web server suffers of “include vulnerability”, users will be able to include any file from any server and those will be executed on your own server.
PHP’s Safe Mode is deprecated in the latest version of PHP, and should not be used anymore. For PrestaShop in particular, having the Safe Mode enabled can render your payment modules useless.
In short, it is highly recommended to have the following directives set to the indicated values:
register_globals = Offmagic_quotes_gpc = Offallow_url_include = Offsafe_mode = Offsafe_mode_gid = Off |
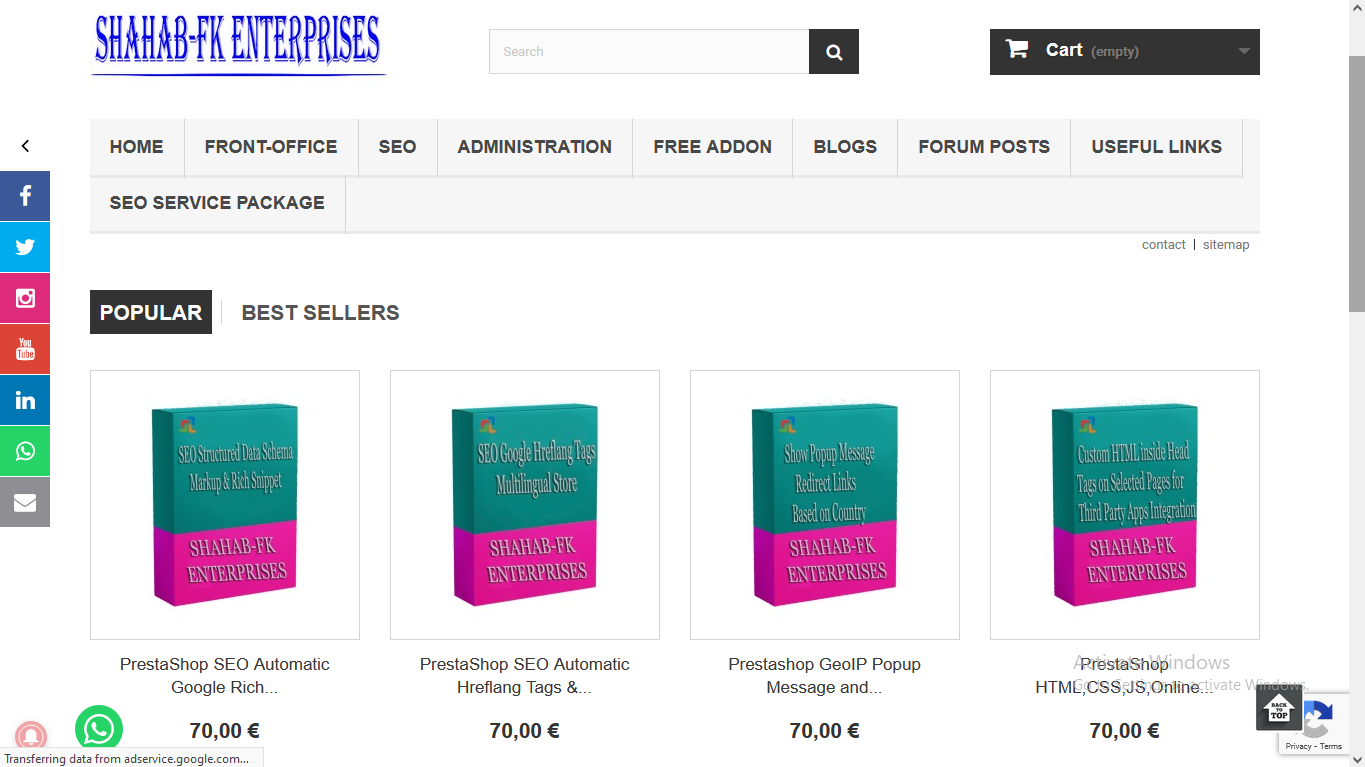
Buy useful prestashop addons magento extensions for online stores
We have extensions in various categories to provide extra features at a reasonable price and the best quality.The modules help to get extra features in online stores and work with all versions. Helps to enhance the performance of the store in different categories like SEO, Security, Analytics, Sales, Social Media, Administration, Marketing, Advertisements, Promotions, etc